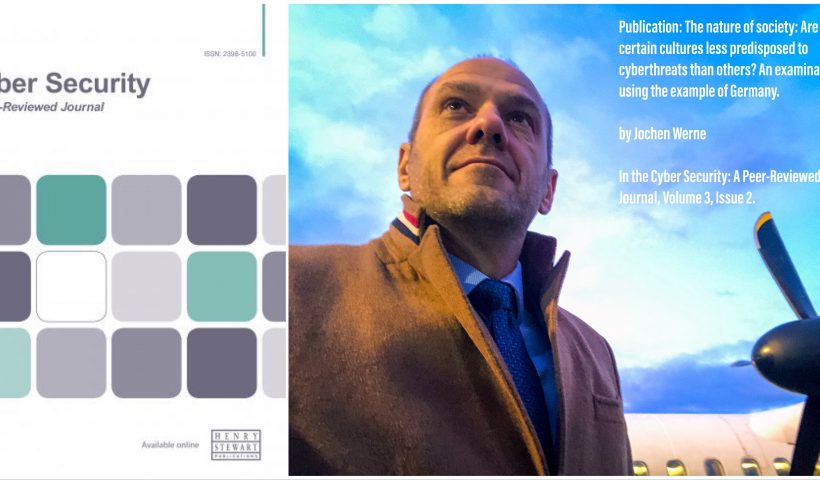
An examination using the example of Germany
Author: Jochen Werne
Published: Werne, Jochen (2019, December 1). The nature of society: Are certain cultures less predisposed to cyberthreats than others? An examination using the example of Germany. In the Cyber Security: A Peer-Reviewed Journal, Volume 3, Issue 2.
ABSTRACT
Successful ransomware attacks and thefts of data and passwords have unequivocally demonstrated that technical defensive measures are to be considered as merely basic moves in the protection against cyberattacks, and that security concepts, if to be effective, must take ever greater account of the human factor. Several examples prove that attack vectors which belong to the area of ‘social engineering’ are menacingly successful. Employees of enterprises, especially SMEs, frequently underestimate their importance when assessing security risks and the defence against them. As a consequence of these findings, a company-wide risk management should respect cultural and psychological peculiarities. Another promising approach are AI-based concepts, both as a technical defence against cyberthreats and in respect of processes specific to the company, as well as culture-specific characteristics of its employees. Both approaches are based on understanding human behaviour in its sociocultural context. Within the scope of this paper, this cultural aspect of cyber security is examined with regard to whether certain cultures may be less predisposed to cyberthreats than others. This is analysed using the example of Germany and also considers the question whether more or less authoritarian company cultures play a role in this context. How can phenomena such as German angst and similar cultural peculiarities be adequately taken into account? The remarks are mainly targeted at an audience which is concerned with organisational and technical countermeasures again cyberthreats. They focus on the importance of incorporating findings from psychology and social sciences when designing and realising such measures.
Author’s Biography
Jochen Werne is the Chief Development and Chief Visionary Officer (CDO/CVO) and executive committee member of PROSEGUR Cash Services Germany Ltd. Prior to that he was director and authorised officer of the Bankhaus August Lenz & Co. AG. Jochen is also member of the Federal Ministry of Education and Research Initiative ‘Learning Systems’ — a platform for artificial intelligence, member of the expert board of Management Circle, as well as a member of one of the most important think tanks worldwide: Chatham House, the Royal Institute of International Affairs. Jochen is a keynote speaker at various banking, innovation and executive conferences as well as an author and co-author of several textbooks and professional articles.
ABOUT Cyber Security: A Peer-Reviewed Journal
Cyber Security is the major peer-reviewed journal publishing in-depth articles and case studies written by and for cyber security professionals. It showcases the latest thinking and best practices in cyber security, cyber resilience, cyber crime and cyber warfare, drawing on practical experience in national critical infrastructure, government, corporate, finance, military and not-for-profit sectors.
Each quarterly 100-page issue analyses significant current and emerging cyber security threats and the latest strategies, techniques and technologies available to detect, manage and react to them, helping to uncover potential weaknesses in your current systems which could be open to attack. Its detailed articles and case studies – all of which are peer-reviewed by an Editorial Board of leading cyber security experts – provide in-depth, actionable advice and ‘lessons learned’ from fellow professionals, showing how cyber security programmes have been specified, designed, implemented, tested and updated in their organisations, as well as how data breaches and exercises have been managed in practice.
Cyber Security does not publish advertorial or advertising but rather in-depth articles on key topics including:
- Cyber security risk assessments, platforms and frameworks
- Building cyber response programmes
- Protective measures
- Threat surface analysis and detection
- Incident response and mitigation
- Training ‘red’ teams
- Crisis and reputation management
- Recovering from a data breach
- Employee and customer awareness, education and training
- Workforce analysis and programmes
- Reporting to senior executives and getting sufficient funding
- Scenario planning, penetration testing and cyber security exercises
- Reducing insurance premiums
- Cyber security in the supply chain
- Insider threats
- Cloud security risk
- Cyber warfare, cyber terrorism and state-sponsored attacks
- Safe disposal of sensitive data
- Cyber security investigations and digital/analogue forensics
- Hackers’ techniques and motivations
- Security architectures and network assurance
- Internet fraud techniques
- Encryption, cryptology and data protection
- User behaviour analytics